In the past few years, the concept of bringing zero-knowledge technologies to the cryptocurrency space, particularly as off-chain and Layer 2 scaling solutions, has gained more traction. Developers have increasingly explored the possibilities that zero-knowledge technologies and validity proofs could unlock for blockchains.
Lately, the conversation about getting zk-proofs live on Bitcoin has been revived with the advent of technologies pointing to zk-rollups and sovereign rollups. The introduction of zk-proofs on Bitcoin could impact everything from Bitcoin consensus to how crypto transactions work on the blockchain.
But what, exactly, are zero-knowledge proofs, and what are the different types of zk- and validity proofs? While existing technologies are very much in the prototype stage for Bitcoin, there certainly is already very strong basis for the role of zero-knowledge technology in scaling Bitcoin.
How Zero-Knowledge Proofs Work?
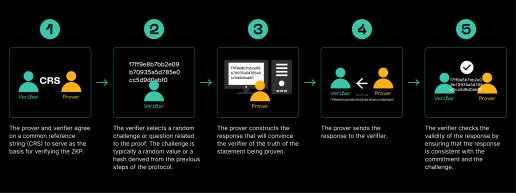
Zero-knowledge proofs (ZKPs or zk-proofs, for short) are cryptographic protocols that allows you to prove and demonstrate knowledge or possession of a particular piece of information to another party (the verifier) without revealing any additional information about it. The concept was first introduced in the 1980s by Shafi Goldwasser, Silvio Micali, and Charles Rackoff.
In a zero-knowledge proof, the prover aims to convince the verifier that a statement or claim is true, without disclosing any underlying data that would prove the statement directly. The proof demonstrates that the prover possesses the knowledge or information required to validate the statement without revealing the actual content.
To achieve this, zero-knowledge proofs rely on advanced cryptographic techniques and mathematical algorithms. They ensure that the proof can be verified by the verifier without any knowledge of the prover's secret or sensitive information. In other words, the verifier gains confidence in the validity of the statement without learning anything beyond its truth.
Source: Trust Machines
Zero-knowledge proofs possess three fundamental properties:
- Completeness: A zero-knowledge proof guarantees that if the statement being proven is true, an honest prover can convince an honest verifier of its truth.
- Soundness: Zero-knowledge proofs ensure that if the statement is false, no dishonest prover can convince an honest verifier otherwise. The verifier's chances of being deceived are negligible.
- Zero-knowledge: The most important property of a zero-knowledge proof is that the verifier gains no additional information or knowledge beyond the validity of the statement. The proof reveals nothing about the prover's secret or sensitive data.
Zero-knowledge proofs find applications across various fields, including cryptography, blockchain, authentication, and secure data sharing. They provide solutions for enhancing privacy, enabling secure transactions, and proving knowledge without disclosing sensitive information.
What are Zero-Knowledge Proofs Used For?
Different types of zero-knowledge proofs have a variety of applications given that they allow users to validate a number of key security and privacy factors, often without trusting a third party. Some of the most common applications of a zk-proof can include:
- Privacy-Preserving Authentication: Zero-knowledge proofs offer a solution for secure and private authentication processes. They can be employed to prove knowledge of a password or other credentials without disclosing the actual password itself. This enables users to authenticate themselves to a system without compromising their sensitive information.
- Blockchain and Cryptocurrencies: ZKPs have gained considerable attention in the realm of blockchain and cryptocurrencies. They allow for efficient and confidential transactions without revealing any transaction details publicly. zero-knowledge proofs, such as zk-SNARKs (Zero-Knowledge Succinct Non-Interactive Argument of Knowledge), have been instrumental in enhancing privacy in blockchain networks like Ethereum.
- Secure Data Sharing: Organizations often face the challenge of sharing sensitive data while maintaining privacy. Zk-proofs offer a solution by enabling secure data sharing protocols. Multiple parties can prove properties of their private data without exposing the actual data itself. This has implications in domains such as healthcare, where sensitive patient information can be shared for research purposes while preserving confidentiality.
- Password and Credential Systems: Zero-knowledge proofs can be applied to password systems to authenticate users without transmitting their passwords over the network. Instead of transmitting the actual password, a prover can convince a verifier of their knowledge of the password without revealing any details about it. This enhances security by mitigating the risks associated with password interception or leakage.
- Secure Cloud Computing: Zk-proofs can also be used to ensure the integrity and privacy of data stored in the cloud. Users can verify that their data is stored correctly on remote servers without exposing the data itself. This enables secure and private cloud computing applications, fostering trust in cloud service providers.
How Do Blockchains Use Zero-Knowledge Proofs?
Zero-knowledge proofs (ZKPs) play a crucial role in enhancing privacy and security on blockchains. They allow for the verification of transactions or computations without revealing the specific details or inputs involved. Here's a simplified overview of how zero-knowledge proofs work on blockchains:
- Confidential Transactions: Zero-knowledge proofs enable confidential transactions on blockchains. In a typical transaction, there are inputs (sources of funds) and outputs (recipients of funds). With a zero-knowledge proof, a prover can demonstrate to the verifier (usually the blockchain network) that the transaction is valid without revealing the specific inputs and outputs. This preserves the privacy of the transaction participants.
- zk-SNARKs: One of the most popular types of zero-knowledge proofs used in blockchains is zk-SNARKs (Zero-Knowledge Succinct Non-Interactive Argument of Knowledge). zk-SNARKs provide a way to prove the correctness of computations without revealing the actual inputs and outputs involved. They allow for succinct and non-interactive proofs, meaning that the proof size is small, and the verification process is efficient.
- Setup Phase: Implementing zero-knowledge proofs on a blockchain typically involves a setup phase. During this phase, a common reference string is generated and distributed. This string is used to generate and verify zero-knowledge proofs. The setup phase ensures the integrity and security of the proof system.
- Generating Proofs: In a blockchain transaction, the prover constructs a zero-knowledge proof to demonstrate that the transaction is valid. This proof is generated based on the transaction inputs, outputs, and the specific zero-knowledge proof scheme being used. The proof is designed in such a way that it reveals nothing about the inputs and outputs, except for their validity.
- Verification: The blockchain network or verifier receives the zero-knowledge proof from the prover. The verifier then verifies the proof using the common reference string and the specific proof verification algorithm. The verifier can efficiently and quickly validate the proof without needing to know the specific inputs and outputs of the transaction. If the proof is valid, the transaction is accepted and added to the blockchain.
- Privacy and Transparency: ZK-proofs on blockchains strike a balance between privacy and transparency. While the specific transaction details remain private, the blockchain still maintains its transparency and immutability. Other participants can see that a valid transaction has occurred without knowing the specific inputs and outputs involved.
By leveraging zero-knowledge proofs, blockchains can achieve enhanced privacy, confidentiality, and security while maintaining the trust and integrity of the overall system. They enable secure transactions and computations on public blockchains while preserving the privacy of participants and their sensitive data.
Unpacking StarkWare zk-STARKs Protocol for Scaling
Zk-STARK (Zero-Knowledge Scalable Transparent Argument of Knowledge) is a type of zero-knowledge proof system that offers scalability and transparency properties. It is a cryptographic construction that allows for the efficient verification of large computations without revealing any intermediate steps or inputs. The system was invented by StarkWare (hence the references to STARK proofs), an Ethereum-scaling firm behind validity-rollup solutions such as Starknet, a zk-rollup protocol that acts as a layer 2 over Ethereum.
StarkWare's protocol was introduced as an improvement over existing zero-knowledge proof systems, such as zk-SNARKs, which require a trusted setup phase and can be computationally intensive. In contrast, zk-STARKs provide transparency by eliminating the need for a trusted setup and offer scalability by enabling the verification of complex computations with lower computational overhead.
Key features of zk-STARK include:
- Transparency: The protocol eliminates the reliance on a trusted setup, making them transparent. This means that the proof generation process does not depend on any secret parameters or authorities, reducing the potential for manipulation or compromise.
- Scalability: zk-STARKs can verify complex computations involving a large number of steps or a large amount of data more efficiently than other zero-knowledge proof systems. This makes them suitable for applications that require handling significant computational tasks, such as blockchain transactions, machine learning, and privacy-preserving computations.
- Post-Quantum Security: The protocol is designed to be resistant against attacks from quantum computers. It utilizes cryptographic techniques that are believed to withstand the computational power of quantum computers, ensuring long-term security.
- Transparency and Auditability: zk-STARKs allow third parties to audit the correctness of the computation being proved without requiring access to the original inputs. This property enhances transparency and allows for independent verification of the claimed results.
While zk-STARKs offer advantages in terms of scalability and transparency, they typically have larger proof sizes and require more computational resources during the verification process compared to other zero-knowledge proof systems like zk-SNARKs. However, ongoing research and advancements aim to optimize zk-STARKs and improve their performance.
Zero-Knowledge Proofs for the Bitcoin Blockchain
While the use of zero-knowledge proofs has been prevalent in newer blockchains such as Ethereum and their layer 2s (like Polygon's Polygon ID project), technology is already being developed to implement zero-knowledge technologies on Bitcoin. For example, there has been increasing conversation about the possibility of how to ensure how to use zero-knowledge proofs to make zk-rollups function on Bitcoin.
Additionally, the ZeroSync Association, a newly formed Swiss non-profit based in Zug with Robin Linus, Tino Steffens and Lukas George as co-founders, also recently announced that they were developing zk-proofs for Bitcoin. As of March 2023, ZeroSync had already produced a prototype that allowed their users to validate the state and transaction history of the Bitcoin blockchain, both of which are down trustlessly. This prototype could also prove the validity of Bitcoin core consensus rules, but not transaction signatures.
Regardless, protocols like ZeroSync's and emerging zk-proof technologies like zk-rollups are already set to impact the Bitcoin blockchain, and even stands to make the case for overhauling network state validation.
Bringing Zero-Knowledge Technology to Bitcoin
Ultimately, the introduction of zero-knowledge proofs to Bitcoin will contribute to the trustless technologies being built upon the blockchain to make it scalable and more efficient. The introduction of these technologies would, essentially, make the Bitcoin network much faster, especially as it would allow developers and users to operate on the network without the trust assumptions that is present in much of technology today.
In the meantime, it's important to keep track of new protocols like the one ZeroSync is using and developing and the emerging development of other technologies like zk-rollups. Together, they contribute to an important chapter of that speaks to Bitcoin's true scalability potential, one that would also introduce a myriad of new use cases for the world's oldest blockchain.