Why We Use Zero Knowledge Proofs for Authentication
Crypto enthusiasts like to talk about how zero knowledge proofs will protect privacy on the internet with better authentication. But everyday users are probably wondering, what do you mean by zero knowledge proof? We’ll explain how cryptographic verification, known as zero knowledge proofs, are key to helping you own your identity.
The Problem With Logins and Passwords
When you use an online application or website, you need a username and password. Today, we all use tens or even hundreds of different apps on a regular basis. This makes keeping track of your logins quite the undertaking.
Instinct probably tells you to use simple, easy-to-remember passwords. But this severely compromises security — which is why most apps now have password strength requirements. Another option is to have a password manager, but this is also inconvenient for the average user. Most people, sadly, have a document or notepad somewhere with all their highly sensitive login credentials.
In addition to users struggling to remember all their passwords, there’s a database security problem. Whether you’re using Facebook, a government website, or your bank account, your account information is in a centralized database. And those databases are owned by each individual app and website.
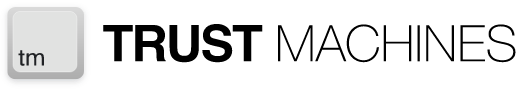
Even if you work hard to secure your data as a user, your private information is still vulnerable. Your bank’s user database could be hacked. Or, your personal info could (and does) get sold by apps like Facebook. This makes people’s trust in centralized organizations to protect their personal information dwindle — and rightly so. Some of the most-used applications like Amazon and Google still haven’t gained the trust of more than 70% of users.
Source: statista.com
ZKPs Can Eliminate Passwords
Zero knowledge proofs (also called ZK proofs or ZKPs) use a cryptographic proof protocol for authentication. And they can be executed on a decentralized blockchain network where data is non-custodial.
This means that instead of being forced to trust every app you create an account on, you can maintain control of your own sensitive information. You don’t need to prove your identity with a password,and you don’t have to remember hundreds of login credentials because the app validating your identity won’t need to see a password.
What is zero knowledge Proof in Blockchain?
Zero knowledge cryptography is a way to prove to another party that you have some secret information without disclosing the information itself. It was developed by Shafi Goldwasser, Silvio Micali, and Charles Rackoff in 1985.
Today, we can use tokens on a public blockchain that are proved with zero knowledge to protect privacy better.
Let’s explain first with a simple example. Imagine there’s buried treasure and you want to prove to your friend you know where it is. A zero knowledge protocol could show you know the secret location of the treasure, but you wouldn’t actually have to tell anyone where it is.
On a blockchain network, zero knowledge encryption can authenticate a user’s identity without revealing any personal information about them.
Do zero knowledge proofs exist?
ZKPs do exist as an encryption system used in different ways. However, they haven’t been completely adopted across the internet yet. But that’s quickly starting to happen.
In the early days of the internet, it was difficult to find things online. Back then, DNS (domain name system) hadn’t been adopted yet. To access anything on the web, you had to locate it using an unreadable string of characters. This is similar to what blockchain addresses look like today.
Once we started using domain names, navigating the internet became much easier and more people could easily find things. Now, you can simply type in something like "wikipedia.com” and the DNS will find its actual location. ENS (Ethereum Name Service) and BNS (Bitcoin Name Service) are starting to do the same thing for blockchain technology.
What is zero knowledge proofs of identity?
With an ENS or BNS address and a zero knowledge blockchain, users will be able to access many platforms using the same identity. Right now, you need a different login identity for every application you use. And even worse — each app owns all of your data and content on its platform.
Twitter owns your identity, profile, content, and influence on Twitter. Google, iMessage, and Discord keep all of your information on their servers. If they want to revoke your access, they can. And very few of these applications are interoperable.
With a global identity like an ENS name that’s protected by ZKPs, users can own their own data and take it with them to any platform. They simply authenticate themselves directly with the blockchain if they know the secret word or key. We’re already seeing this happen with ENS integrations on platforms like Console.
How Do You Make Zero Knowledge Proofs?
Using zero knowledge proofs involves a prover and a verifier. The verifier checks if a statement is true using a computation whose odds leave very little chance the prover is lying. In the zero knowledge proof example below, Bob is trying to verify that Alice knows the code to unlock the door inside a cave.
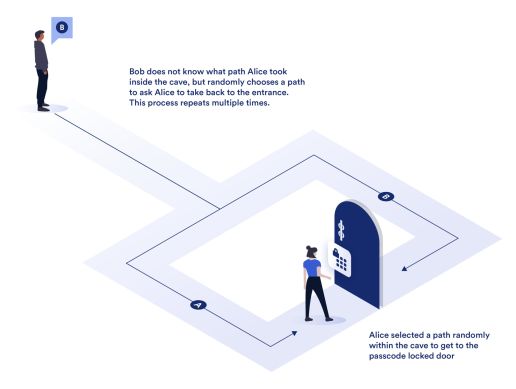
Source: blog.chain.link
Once Alice is inside the cave, Bob tells her one of multiple ways to get out, which lead her through the locked door. If Alice is able to return to Bob multiple times in a row, no matter which path he chooses, it will prove the soundness of Alice’s claim that she knows the code. But Alice never reveals the code and Bob never knows which path Alice took to get inside the cave.
This ability to prove knowledge of a secret is true without using traditional authentication systems — like passwords — increases privacy and security. And the computational process happens instantly in a zero knowledge proof system. There are also different ZK proof applications that require different types of ZKPs.
Types of ZK Proofs
Interactive zero knowledge Proofs
An interactive proof system performs multiple interactions to verify the soundness of another party’s claim on transaction data without revealing the data itself. The example of Bob and Alice uses interactive ZKPs.
Non-Interactive Zero Knowledge Proof
A non-interactive proof only allows one transaction to verify the prover. Some blockchains use them for things like proving a wallet has enough funds to send a transaction without revealing the actual balance.
zk-SNARKs
This stands for "zero knowledge Succinct Non-Interactive Argument of Knowledge." These ZKPs require a trusted setup and creating a set of crypto keys. They also don’t require interaction between the verifier and prover.
How Are Zero Knowledge Proofs Used?
Why do we need zero knowledge proofs?
Identity Verification
A great benefit of zero knowledge protocols is identity verification. Imagine if chat apps used ZKPs when you login. Instead of entering a username and password as authentication information, your identity off-chain could be verified with the zero knowledge proof protocol without revealing your real life identity.
Logins
Decentralized chat apps like Console can improve security, but zero knowledge proofs work to improve user experience too. If you don’t have to input credentials every time you want to use Console, you’ll never have to scramble to find them. Nobody likes losing a password!
Token gating
If you want to create a community of people who own certain cryptocurrencies or NFTS, this becomes easy. A verifier could quickly be able to prove a new user holds certain tokens before they’re able to join. And the process never compromises user privacy.
Global identity
Zero knowledge proof blockchains can also become useful outside the crypto world. A single, ZKP identity could be used for all applications across the internet. This hasn’t become a norm yet, but things like ENS and BNS are making it possible.
Global Identity is the Future
So, what problem does a zero knowledge proof best solve? The answer is big and complex, yet very simple: it will allow users to be back in control of their own personal information. People don’t fully grasp the extent to which their data is not their own,and this norm is so interwoven in our online existence that it’s nearly inextricable.
But projects like Console are talking about and actively changing that with trustless, decentralized, and cryptographically protected information. Everyday people can take back control of their information. And we can all finally stop creating and forgetting a million passwords for every single app we want to use!